To have MFA enabled also in a B2B scenario is important. But it could lead to two MFA prompts which could lead to the MFA fatigue syndrom. In this post I will show you how you could reduce MFA prompts.
Introduction
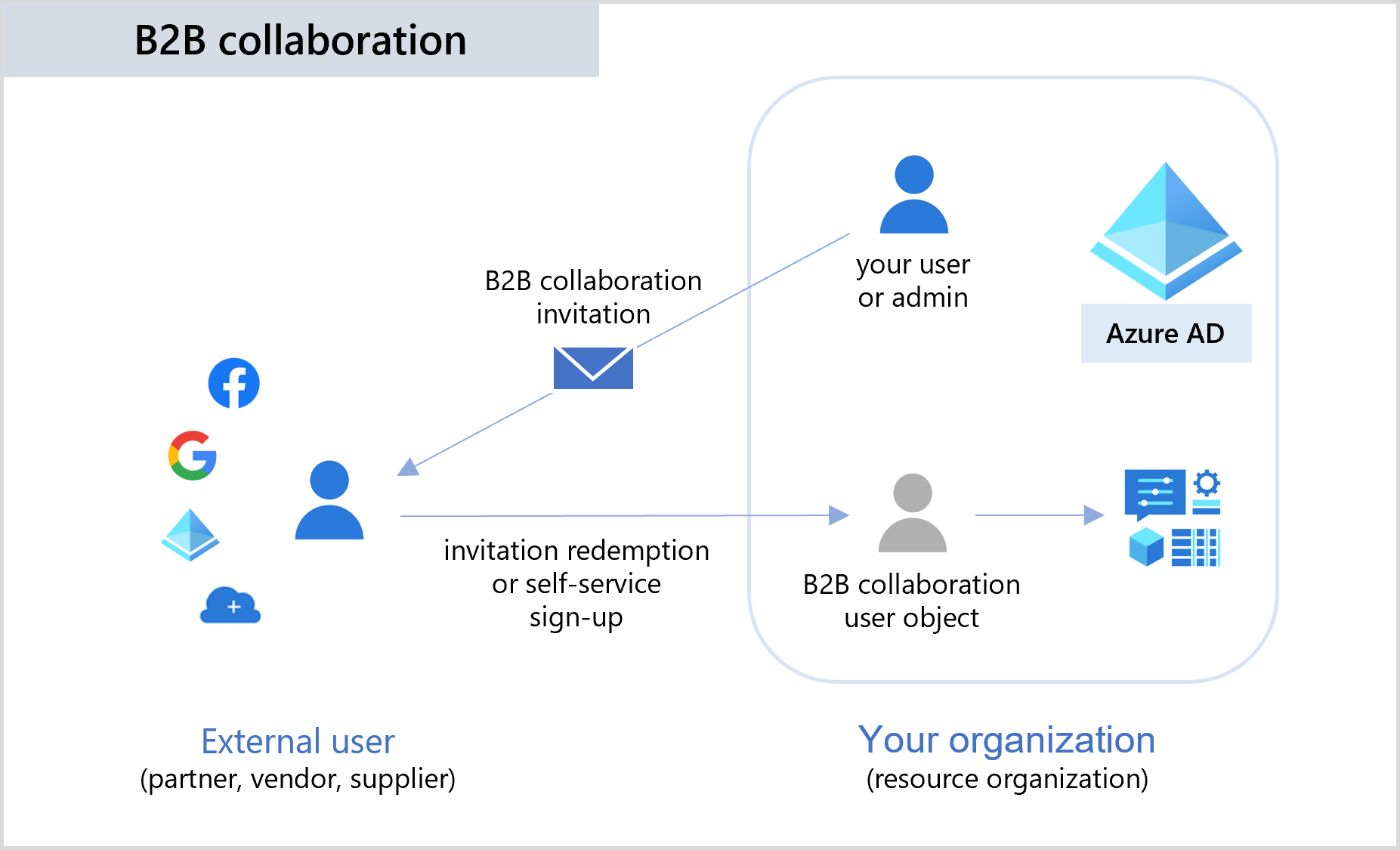
In a modern world collaboration is happening all the time. For this purpose B2B collaboration will be used. In simple terms it allows you to invite users to your own tenant and use ressources of them.
To protect your tenant it is common to enforce MFA by using Default Security Setting or alternative by using Conditional Access policies.
The “issue”
Of course your collaboration partner also protects his tenant with MFA enforcement. From a user point of view this lead to following authentication flow when he tries to access a ressource in your tenant (and is currently not authenticated):
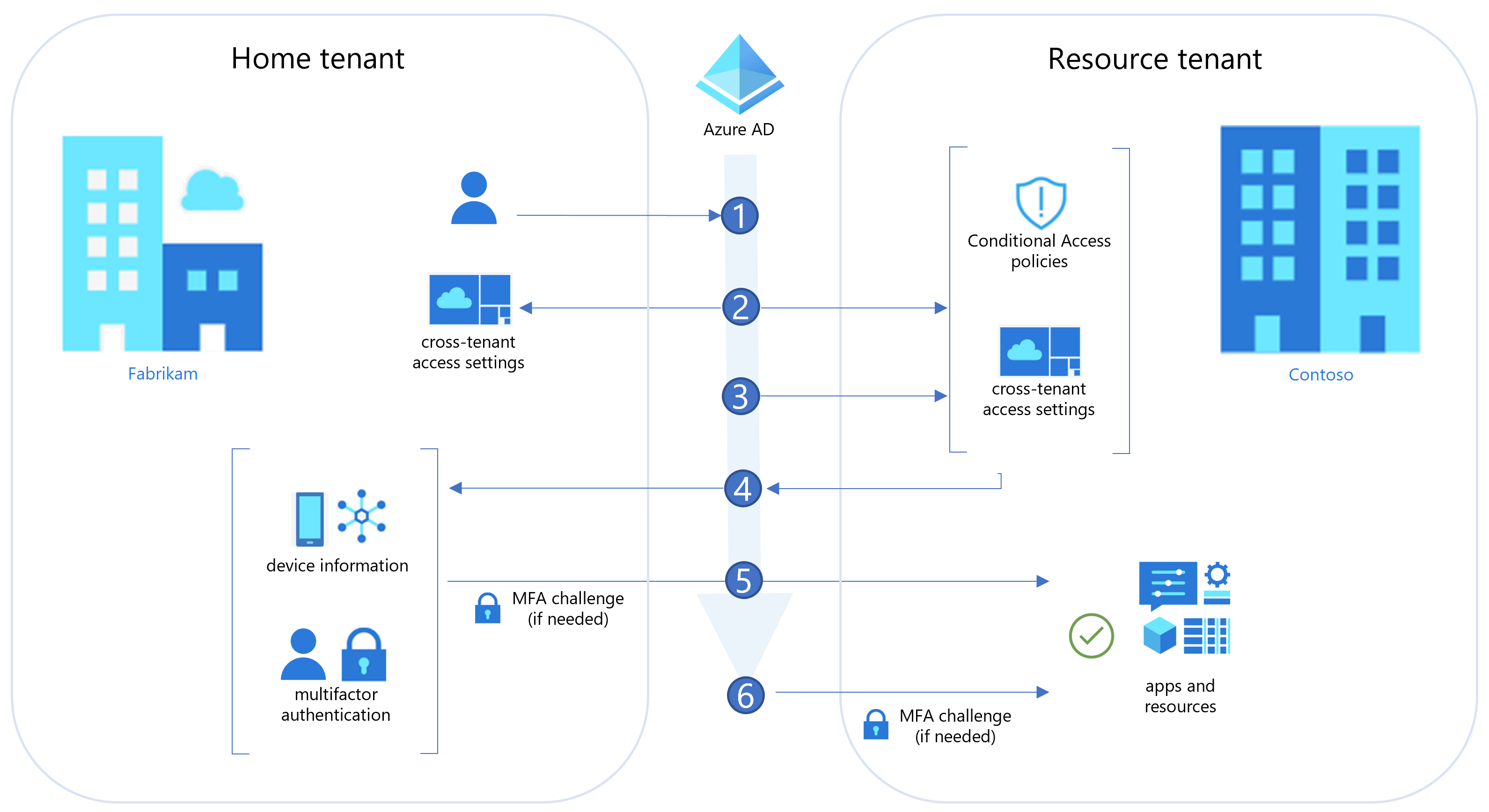
graph TD A[User] --> B(Calling Resource in Resource Tenant) B --Redirect to Home Tenant--> C(Authentication in Home Tenant) C --> D(MFA in Home Tenant) D --Redirect back to Resource Tenant--> E(Authentication in Resource Tenant) E --> F(MFA in Resource Tenant) F --> G(Access to resource) subgraph Home Tenant C D end subgraph Resource Tenant E F end
As showed the user is prompted twice for an MFA:
- When authentication is done in the Home Tenant
- Again when the user tries to access a resource in the Resource Tenant
Other “issues”
Beside of the “multiple” MFA requests you will also get additional “issues”. Think about you are a service provider and working for multiple customers. What happens when you have to replace your MFA token (aka your mobile)? Yes; you have to enroll MFA not only in your Home Tenant but also on every Resource Tenant you have access to. A very time consuming process.
The solution
To reduce the amount of MFA requests and also avoid multiple MFA re-register tasks the Resource Tenant could be configured to trust the MFA settings of the Home Tenant of the user (mark Trust multifactor authentication from Azure AD tenants).
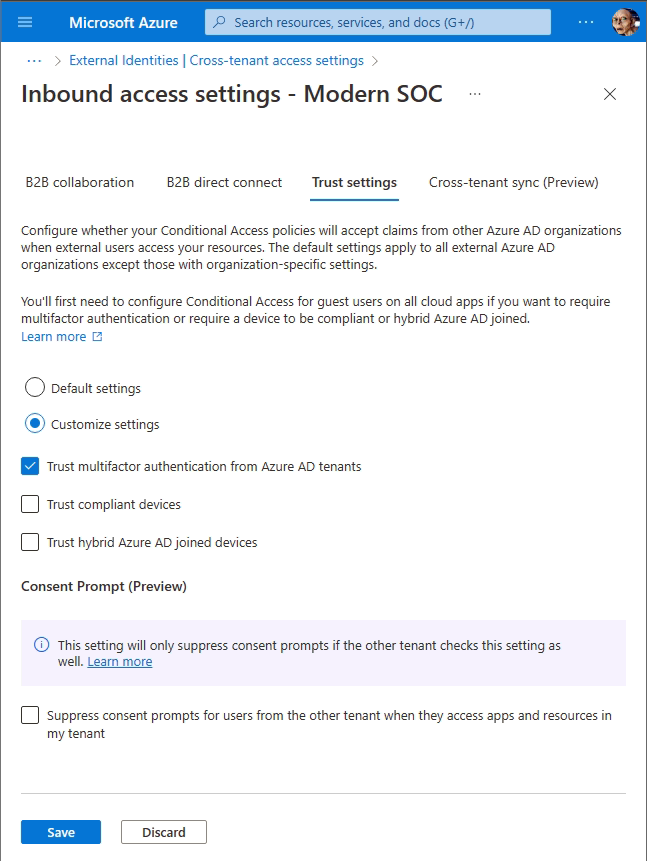
With this setting applied a user has to supply MFA only once - independent if the Home Tenant or the Resource Tenant has MFA enforced.
- If Home Tenant has no MFA enforced, MFA will be requested in Resource Tenant (also enrolled there).
- If Home Tenant has MFA enforced, Resource Tenant will trust and not ask for MFA again.
- If the user has to replace his MFA token, it is sufficient to replace it in the Home Tenant; due Resource Tenant trusts the MFA there was no MFA token enrolled in the Resource Tenant so also no replacement is required.
Drawback of this solution:
- Each Resource Tenant has to implement settings to trust the Home Tenant.
Links
Detailed description of those B2B collaboration settings can be found here: https://learn.microsoft.com/en-us/azure/active-directory/external-identities/authentication-conditional-access#authentication-flow-for-external-azure-ad-users