Microsoft provides an Enterprise Attack Surface Management (EASM) tool. In this blog series I want to disover the tool and the possibilities. This is part 1 of an upcoming series.
Introduction
From a security point of view it is important to know how the external attack surface of the company looks like. For this purpose several tools exist. In typical scenarios a simple vulnerability scanner is used to discover weaknesses in your external surface.
The main issue with such tools is that you need to know what your external surface is - furthermore changes are not automatically updated so you often miss important things in your external surface.
Here comes External Attack Surface Management (EASM) to the rescue. Those tools should help to discover with intelligent information gathering assets which could belong to your external surface.
This blog series will discover the possiblities of the Microsoft External Attack Surface Management tool which you can activate in your Microsoft Azure Tenant. The series consist of following articles:
- Basic Setup and Check first results (this article)
- How to tune Microsoft Defender EASM after first discovery
- Comparison with other known tools
Let’s get started
The initial setup of EASM is easy and is done with following simple steps:
- Have a subscription ready
- Create a resource group
- Deploy Microsoft Defender EASM into defined resource group
- Define first artifacts as starting point of the discovery process
- Wait 48 hours (Yes, it takes really two days until you get first results)
Deploy Microsoft Defender EASM
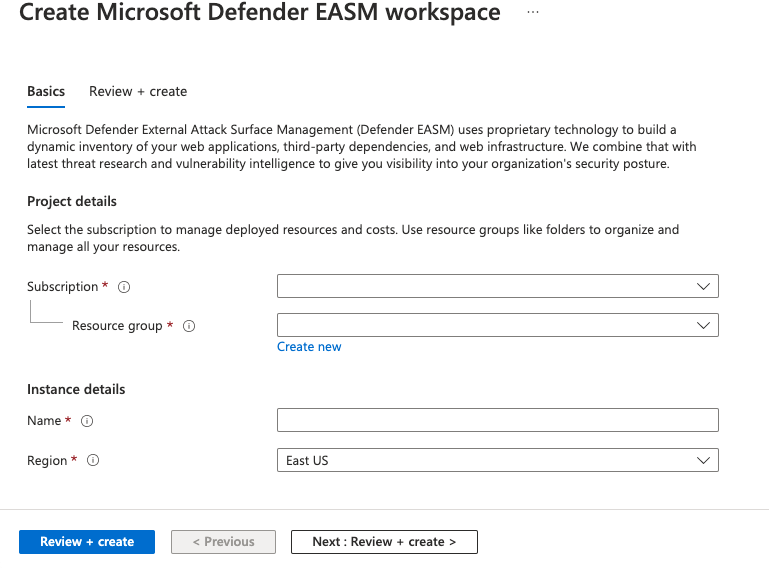
Deployment of the Microsoft Defender EASM workspace is easy as other workload in Azure:
- Just invoke the wizard by searching for EASM in the search bar in the Azure portal
- Fill in details: Subscription (here
Visual Studio Enterprise Subscription – MPN), Resource Group (in my examplerg_Security), a name for your EASM workspace (referenced aseasmin the article) and region (East US) - Hit on
Review + create(and finally onCreate)
Define first artifacts
To get started you have to define data for your first disovery run. You have the following possibilities (not all have to be filled with information):
- Organisation Namen
- Domains (Includes)
- Domains (Excludes)
- IP Blocks
- Hosts
- Email Contacts
- ASN
- Whois Organizations
For my first run I just filled in following information (please adapt those for your environment):
- Organisation Namen
EisenechericERModern-SOC
- Domains (Includes)
icer.cheisenecher.chmodern-soc.ch
- Hosts
remote.eisenecher.ch
Adjustments can be done after the first run so if you forgot something it’s not an issue.
Wait for 48 hours
Now you have to wait until the first run is done. This takes up to 48 hours. Until then you will just see a default screen telling you that discovery is ongoing.
First Results
Now 48 hours passed by and results are available in my EASM instance. I will go through the results and will discuss the findings which the tool presents.
Overview
You will get a nice dashboard over your external attack surface - just go to your enrolled easm workspace and you will see something like this:
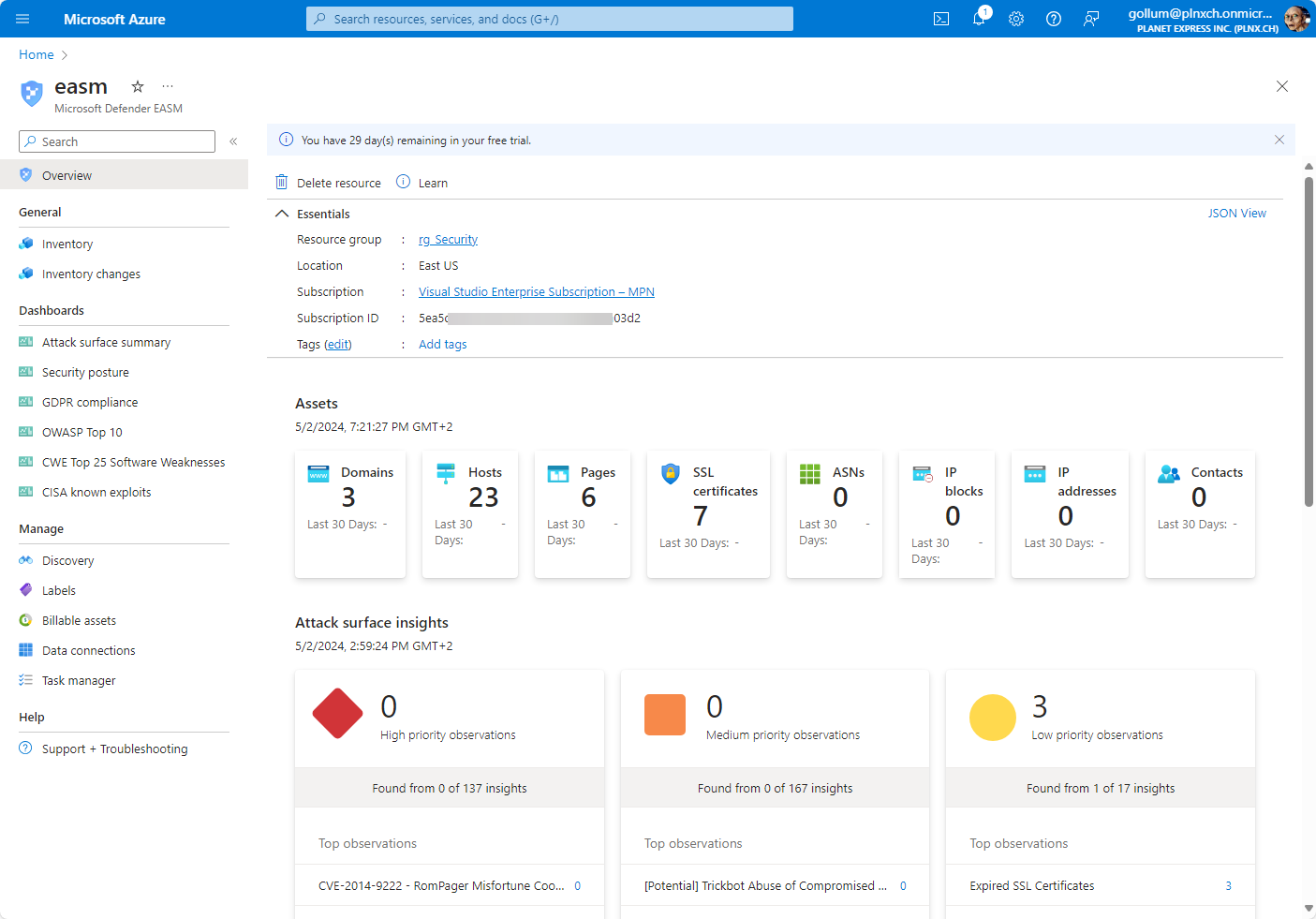
As you can see the results are grouped by following topics:
- Domains
- Hosts
- Pages
- SSL certificates
- ASNs
- IP blocks
- IP addresses
- Contacts
For further explanation I explore the section Hosts only.
Host Details
As an example here a screenshot of the hosts: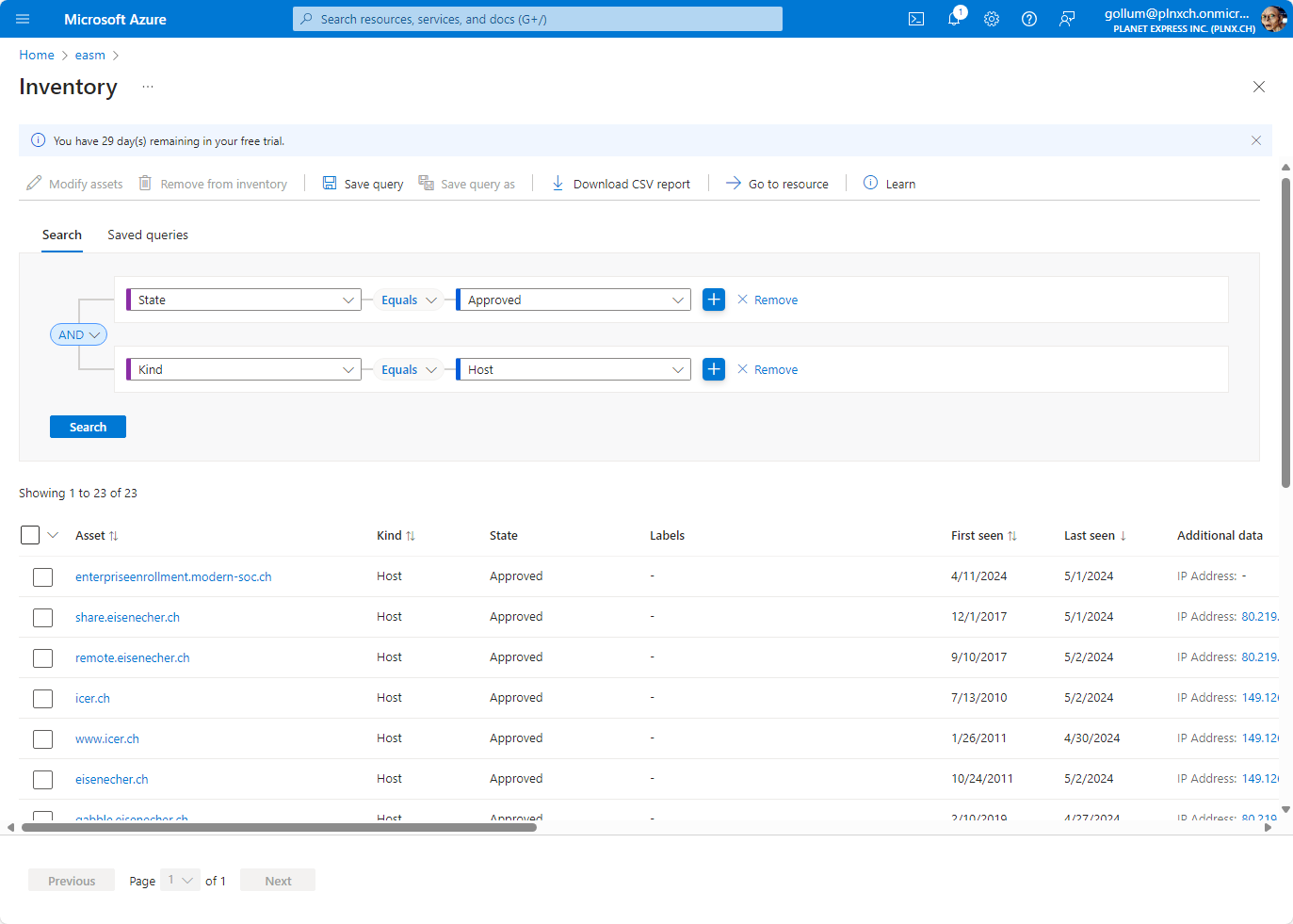
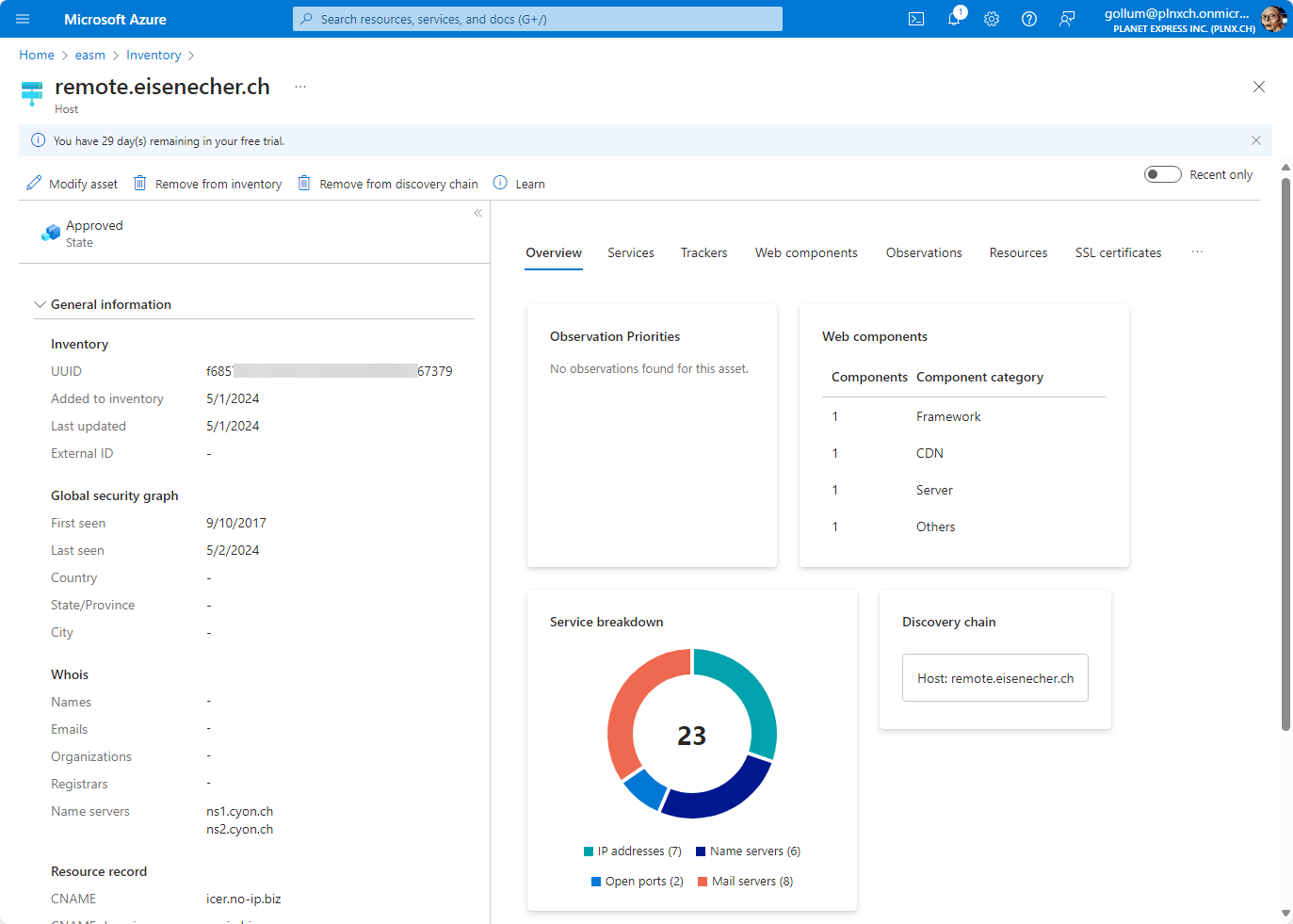
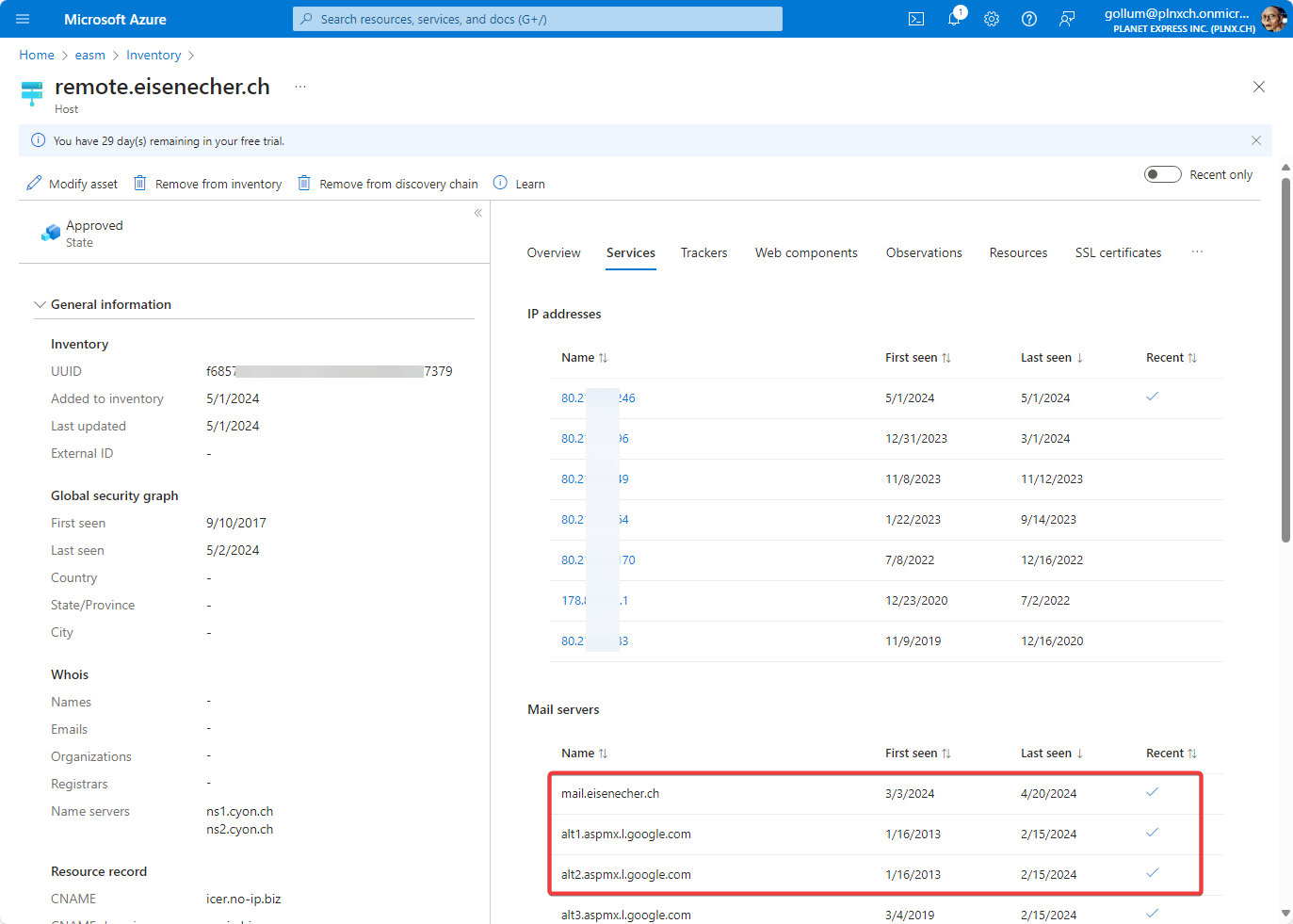
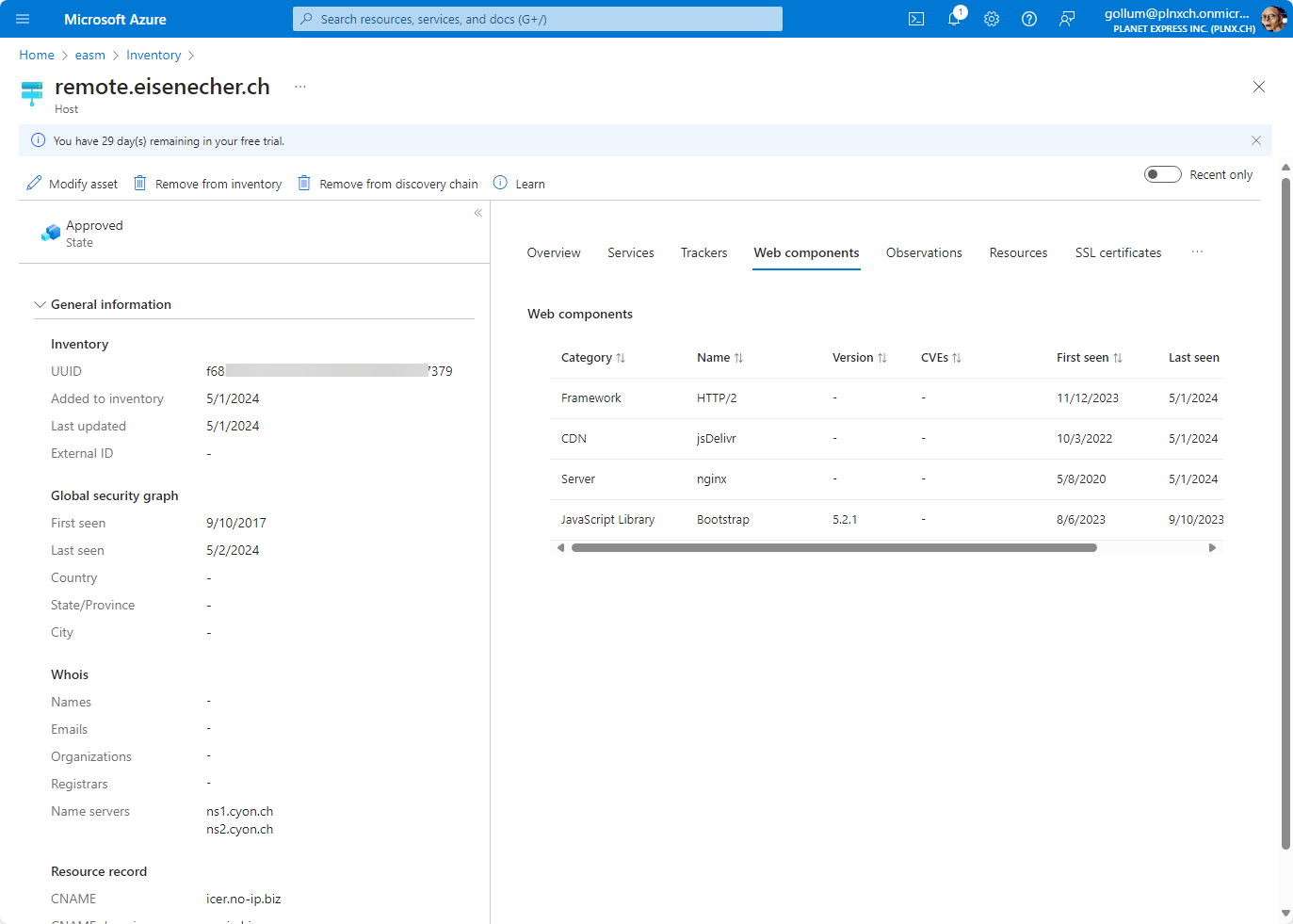
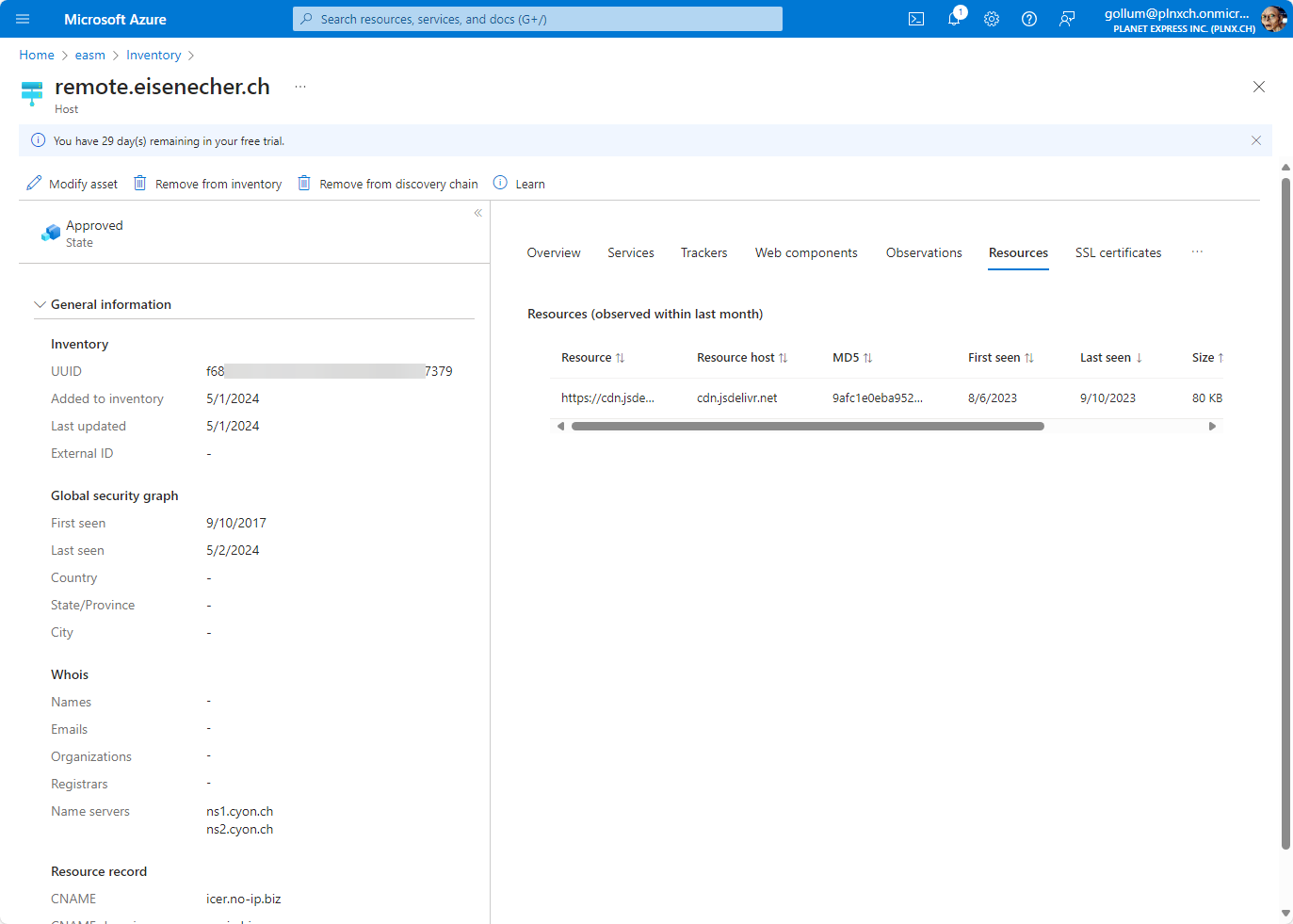
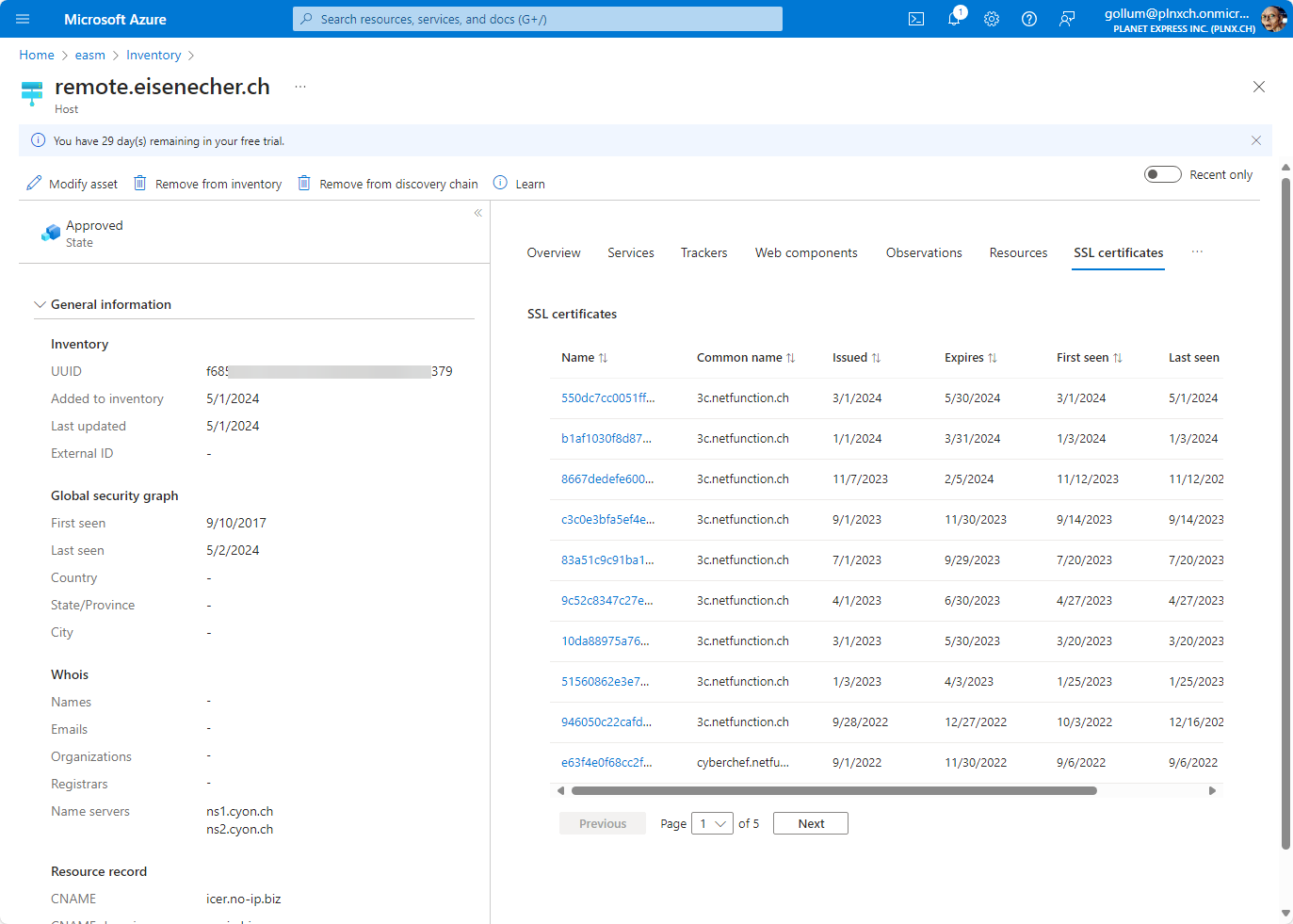
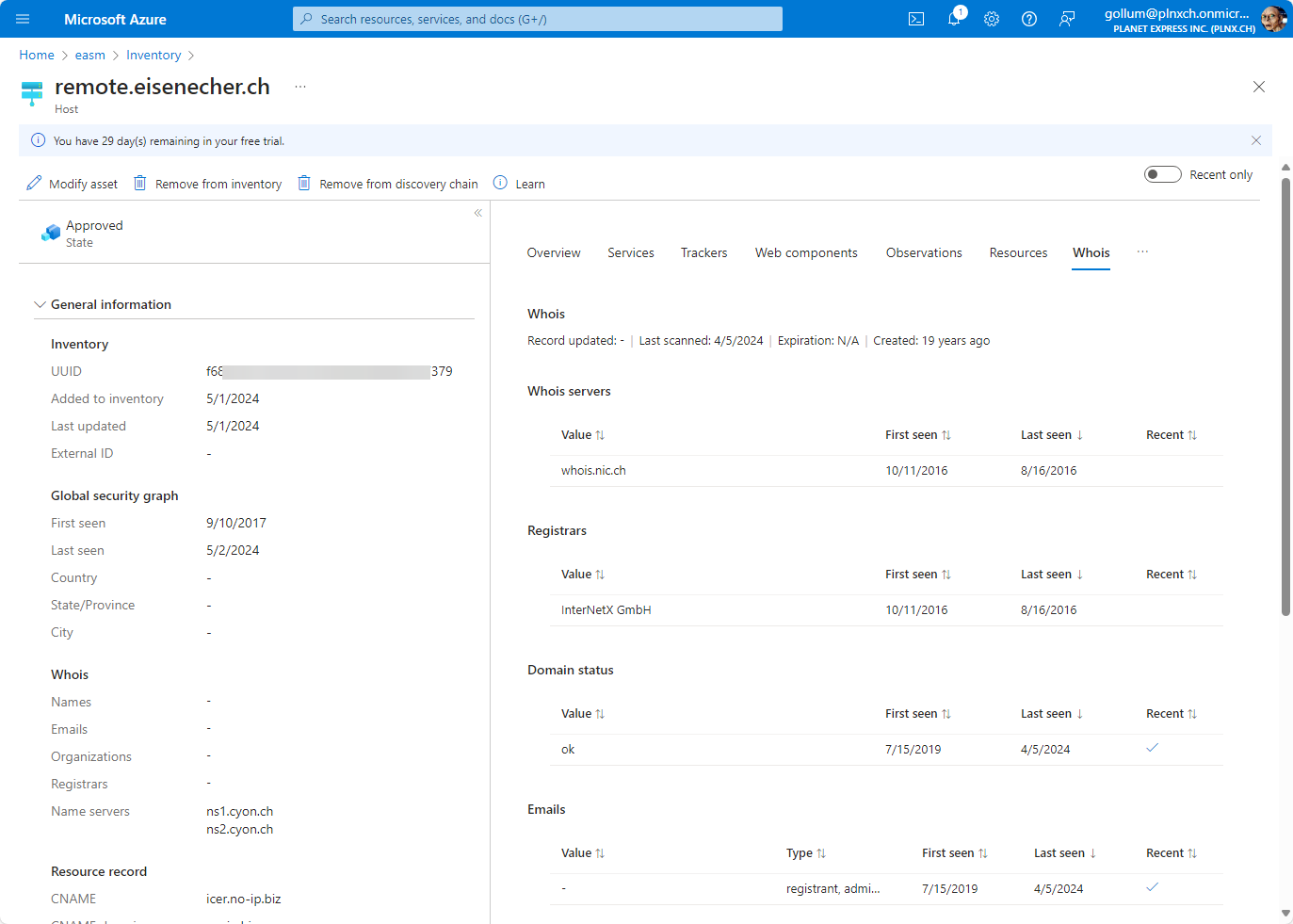
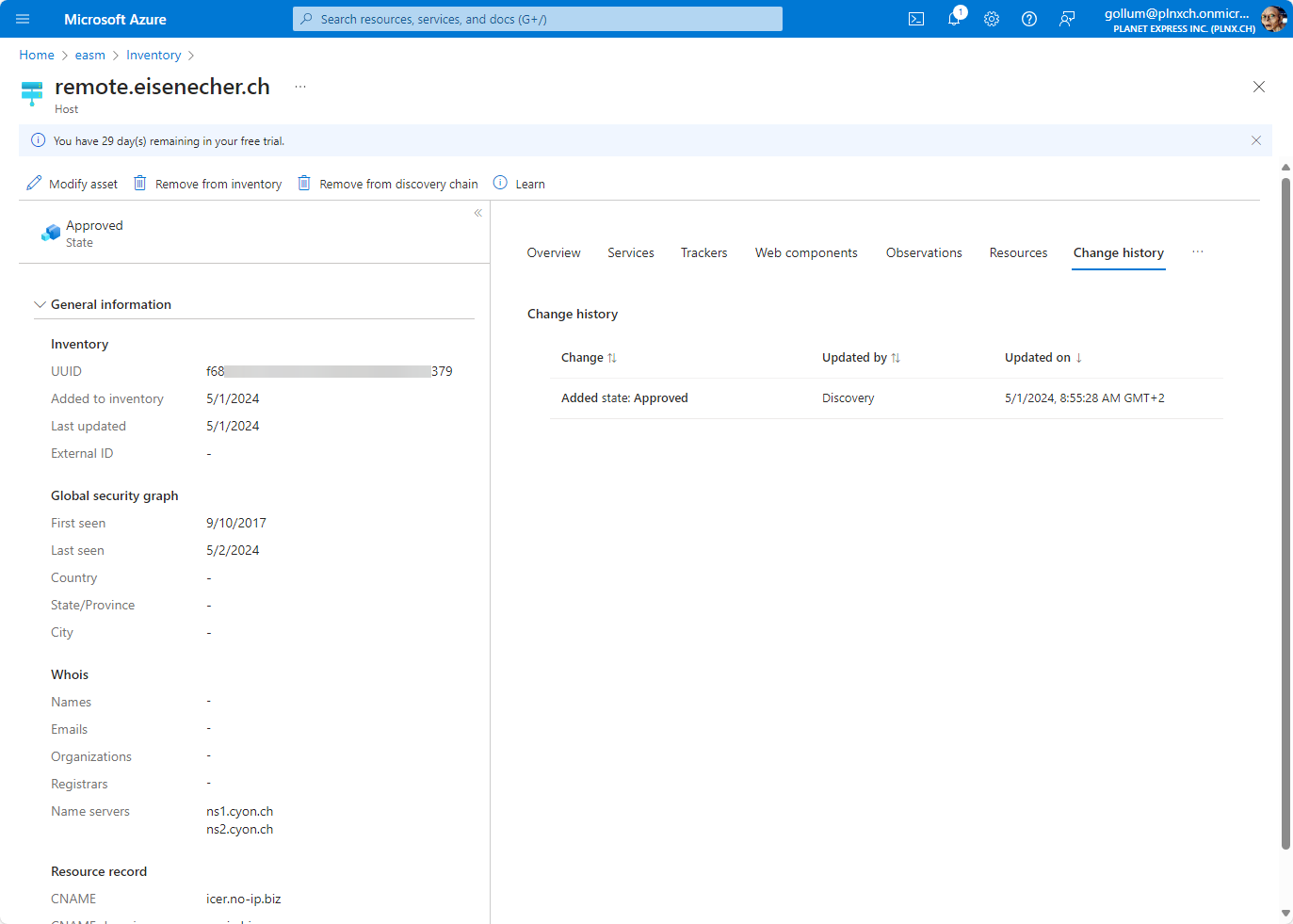
remote.eisenecher.ch) we initially specified in the discovery page, EASM found additional hosts which belong to your assets. Beside of the name you get additional information like IP address, corresponding DNS servers, when the name was first and last seen. If you click now on the host you get details about the host. Here are screenshots of the details EASM discovered:
Attack Surface Insights
Below of that overview you will get a prioritiesed list of observed artifacts:
- High
- Medium
- Low
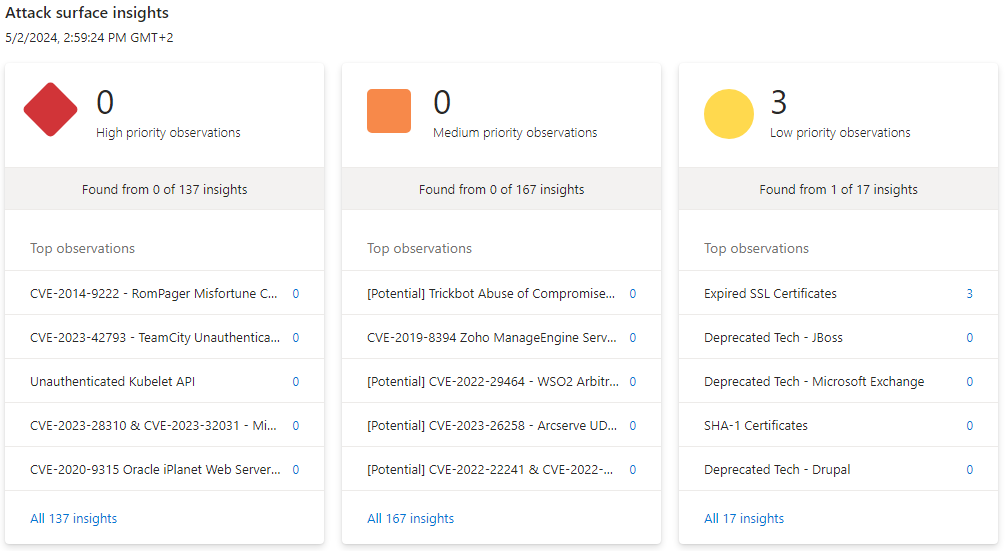
EASM Attack Surface Insights sorted according priority.
In the screenshot it looks like there is an issue with priority low: Expired SSL certificates. If you click on it you get more insight about the finding: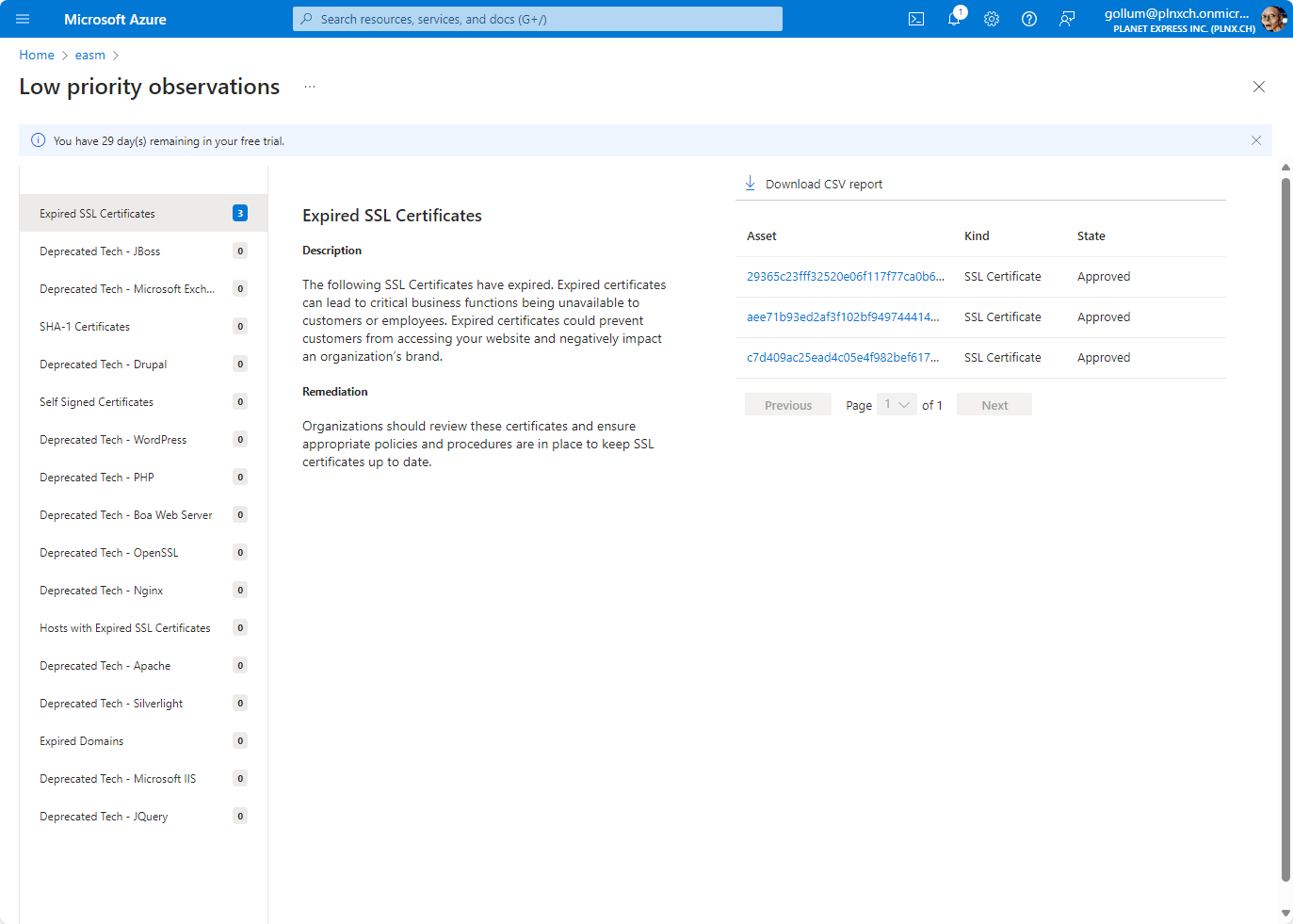
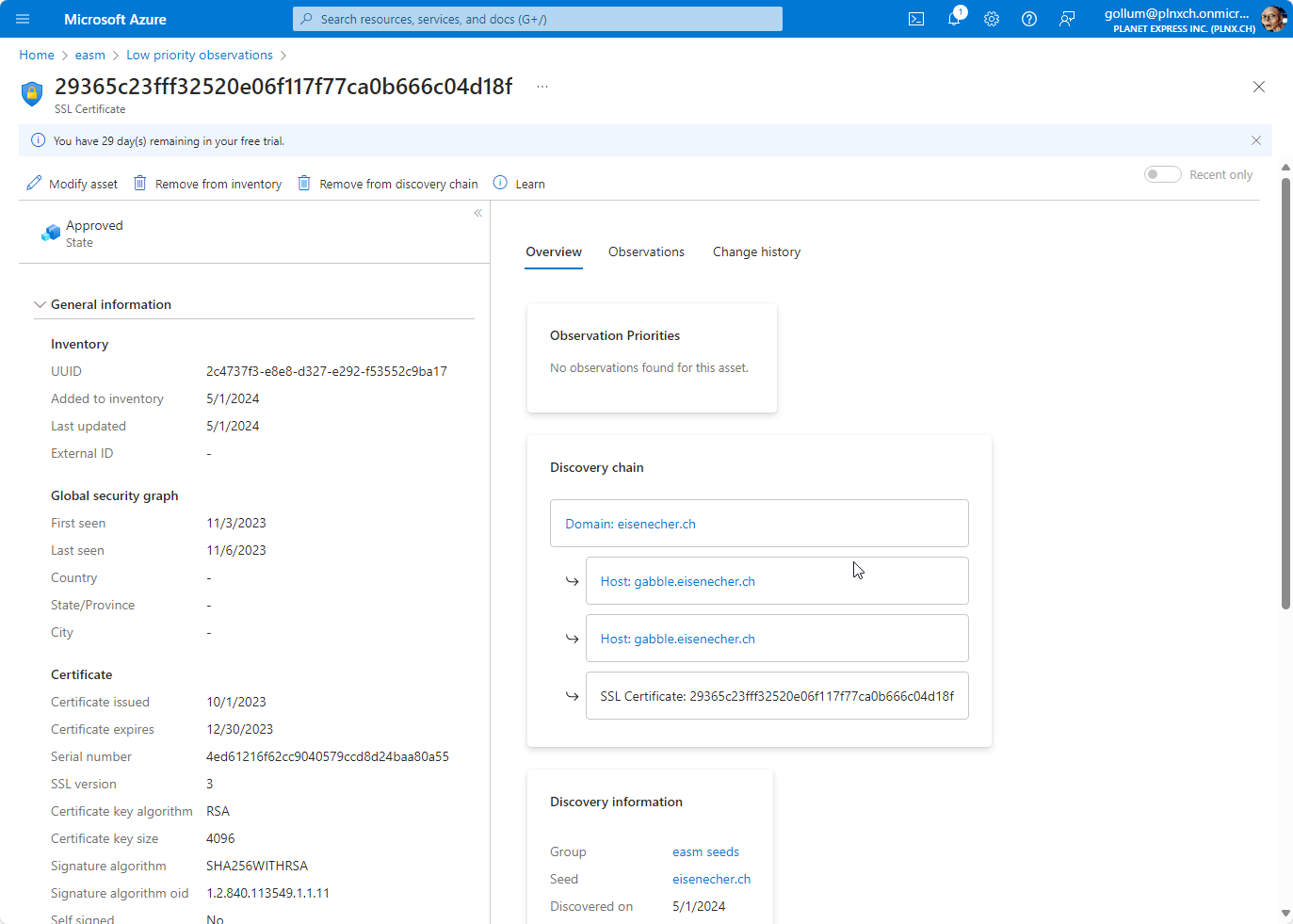
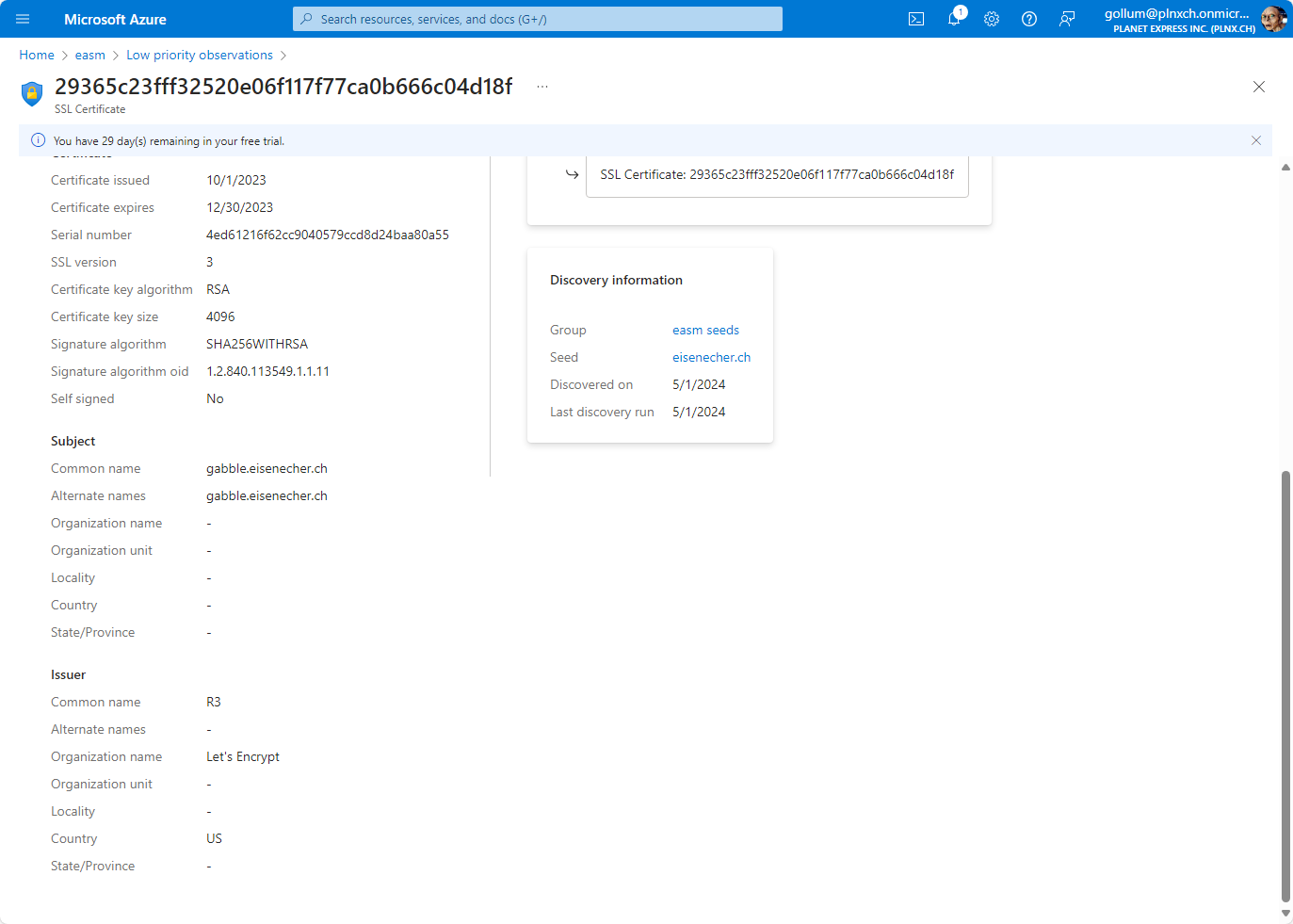
But this shows you also that EASM not only checks for actual observations (EASM was setup on 30.04.2024, results where available on 02.05.2024) - but also looks back in time (the entry shows details from the timeframe 03-06.11.2023).
Costs
According to the documentation of Microsoft each approved asset (Domain, IP address, Host) will be billed for $0.011 per day. According to the overview shown before and without further tuning we have following billable assets:
- Domains: 3
- Hosts: 23
- IP addresses: 0
The estimated cost will be (3+23+0) x $0.011 x 30 = $8.58/month ($102.96/year)
Good to know: The first time you activate Microsoft Defender EASM you will get a free 30 day trial - so it is easy to check the tool if it is suitable for your needs.
Summary
After the first review of the observations the results are mixed. As detailed above EASM shows information about your external surface and combines it with historic data so you see the development of your external surface over time. On the other hand you also saw that EASM complained about expired certificates which are already replaced. With that the supplied information has only a limited value.
This are the first thoughts about Microsoft Defender EASM. Please check out future blog posts regarding EASM with more details.
Further Reading
Here are some links:
- Microsoft Defender EASM Overview: https://learn.microsoft.com/en-us/azure/external-attack-surface-management/